Does the VPN Know as a Virtual Private Network 2024?

VPN (Virtual Private Network) refers to the ability to establish a secure network connection when using public networks. VPNs encrypt your internet traffic and conceal your identity online. This makes it more difficult for third parties to track your online activities and steal information. The encryption happens in real-time.
How Does A VPN Function?
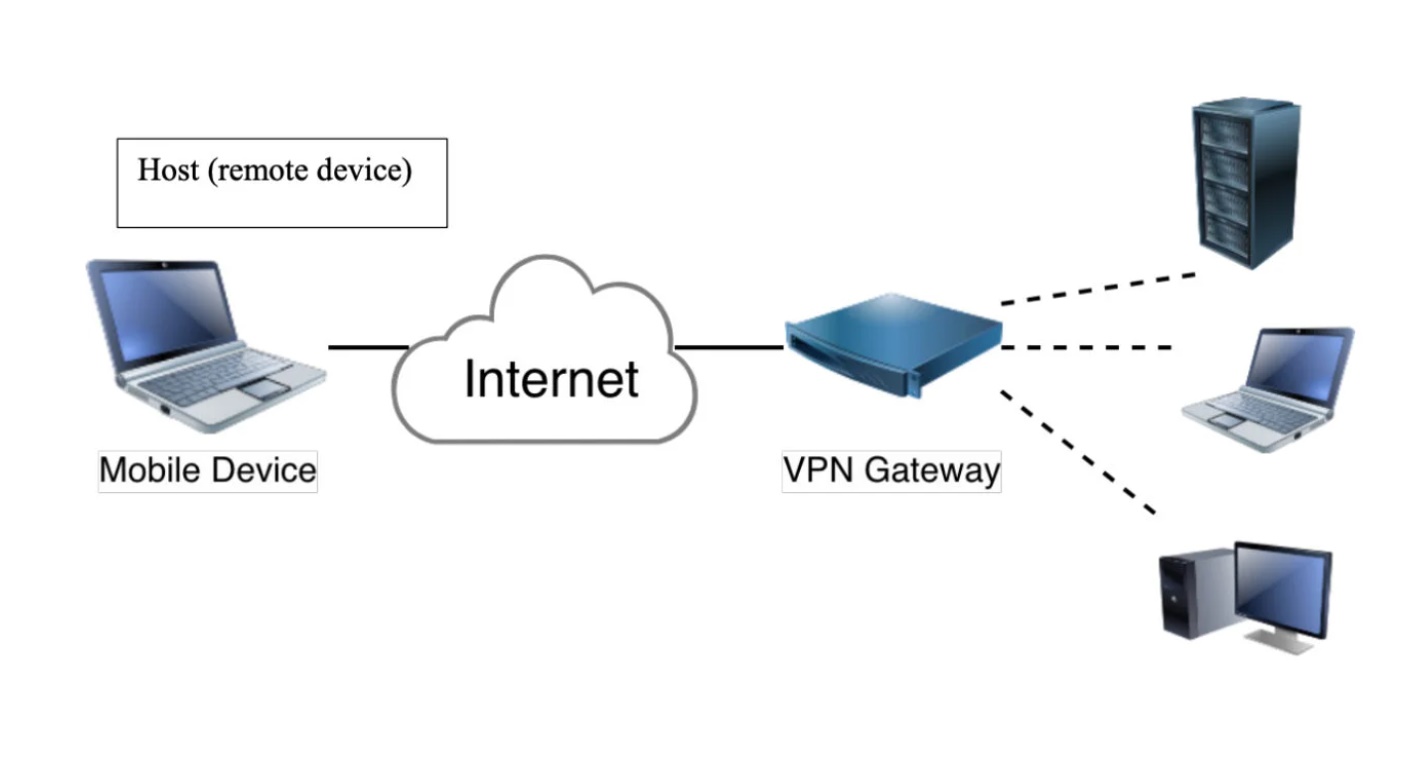
A VPN conceals your IP address by routing it through a specially configured remote server run by a VPN host. This means that if you use a VPN to surf the web, the VPN server becomes the source of your data. This means that your ISP and other third parties cannot see which websites you visit or what data you send and receive online. A VPN acts as a filter, converting all of your data into “gibberish.” Even if someone were to obtain your data, it would be useless.
What Are The Advantages Of Using A VPN Connection?
A VPN connection masks your online data traffic and protects it from prying eyes. Anyone with network access and a desire to view unencrypted data can do so. Hackers and cyber criminals are unable to decipher this data when using a VPN.
Secure encryption: To read the data, an encryption key is required. Without one, it would take a computer millions of years to decipher the code in the event of a brute-force attack. Your online activities are hidden even on public networks with the help of a VPN.
Disguising your location: VPN servers essentially serve as proxies on the internet. Your exact location cannot be determined because the demographic location data is obtained from a server in another country. Furthermore, most VPN services do not keep logs of your activities. Some providers, on the other hand, record your activity but do not share it with third parties. This means that any potential record of your user behavior is forever hidden.
Access To Regional Web Content:
Regional web content is not always available from all locations. Services and websites frequently contain content that is only available in certain parts of the world. To determine your location, standard connections use local servers in the country. This means you can’t access content from your home country while traveling, and you can’t access international content from your home country. With VPN location spoofing, you can “change” your location by connecting to a server in another country.
Secure data transfer: You may need to access important files on your company’s network if you work remotely. This type of information necessitates a secure connection for security reasons. A VPN connection is frequently required to gain network access. To reduce the risk of data leakage, VPN services connect to private servers and use encryption methods.
Why Should You Connect To A VPN?
When you connect to the internet, your ISP usually configures your connection. It follows you using your IP address. Your network traffic is routed through the servers of your Internet service provider, which can log and display everything you do online.
This is especially important if you use public Wi-Fi networks frequently. You never know who is watching your internet activity or what they might steal from you, such as passwords, personal information, payment information, or even your entire identity.
What Functions Should A Good VPN Provide?
You should use your VPN to complete one or more tasks. The VPN should also be secure against compromise. A comprehensive VPN solution should include the following features:
IP address encryption: The primary function of a VPN is to conceal your IP address from your ISP and other third parties. This allows you to send and receive information online without worrying about anyone else seeing it except you and the VPN provider.
Protocol Encryption:
A VPN should also prevent you from leaving traces, such as your internet history, search history, and cookies. Cookie encryption is especially important. It prevents third parties from accessing confidential information such as personal data, financial information, and other website content.
Kill Switch: If your VPN connection is suddenly terminated, your secure connection will be terminated as well. A good VPN can detect this unexpected downtime and terminate pre-selected programs, reducing the possibility of data compromise.
Authentication with two factors: A strong VPN checks everyone who attempts to log in using a variety of authentication methods. For example, you may be asked to enter a password before receiving a code on your mobile device. This makes it uninvited third parties difficult to gain access to your secure connection.

VPN stands for “Virtual Private Network” and describes the opportunity to establish a protected network connection when using public networks. VPNs encrypt your internet traffic and disguise your online identity. This makes it more difficult for third parties to track your activities online and steal data.
Finally, thanks for staying with us, if you know anything about Does the VPN Know as a Virtual Private Network. Then you can tell us your opinion in the comments below.